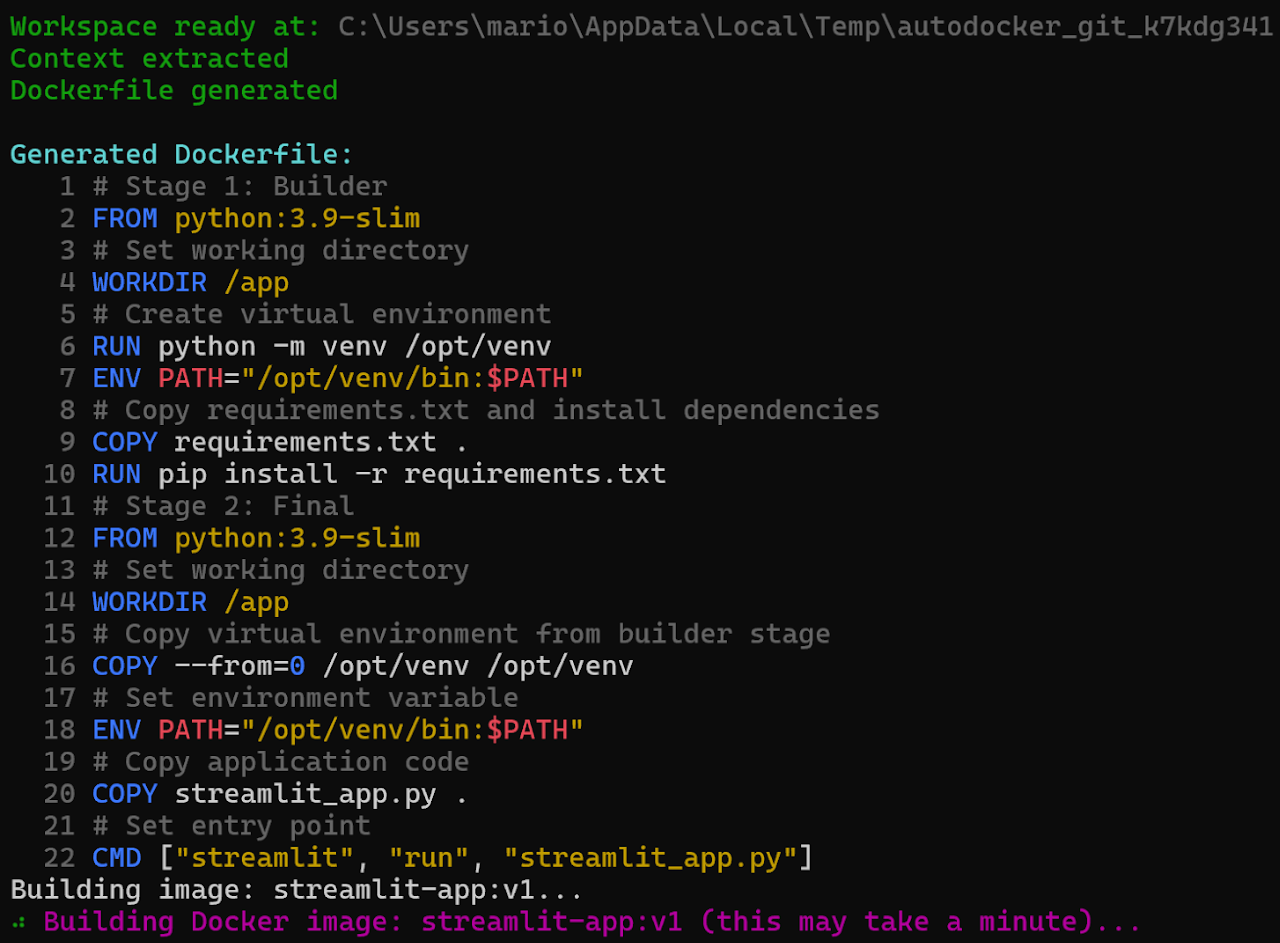
Python CLI for intelligent Dockerfile generation with self-healing builds
Architected a containerization automation CLI in Python using LiteLLM for intelligent Dockerfile generation with a self-healing algorithm that auto-diagnoses and retries Docker API builds based on project-specific context. Logic-driven CLI using Rich and Argparse with real-time build status tracking, automated runtime stability testing, and support for distroless/Alpine multi-stage builds to minimize attack surface.
Case Study
Problem
Eliminate the manual, error-prone process of writing Dockerfiles by generating, building, and self-healing them automatically from project context using an LLM.
Architecture
- Python CLI built with Rich + Argparse for UX and progress feedback
- LiteLLM abstraction layer for pluggable LLM backends (OpenAI, local, etc.)
- Project-context extractor that reads directory structure and config files
- Self-healing loop: build → diagnose failure via LLM → patch → retry
- Runtime stability tester (container smoke test after successful build)
- Distroless and Alpine multi-stage build templates to minimise attack surface
Challenges
- Prompting the LLM to produce deterministic, valid Dockerfile syntax reliably
- Distinguishing transient Docker daemon errors from structural Dockerfile errors
- Avoiding infinite retry loops without hard-coding a fixed number of attempts
- Supporting diverse project structures (Node, Python, Go, etc.) with one prompt strategy
Tradeoffs
- Chose LiteLLM over a direct OpenAI SDK call to stay provider-agnostic
- Accepted non-determinism in LLM output in exchange for higher-quality Dockerfiles
- Self-healing loop is bounded by a configurable max-retries flag rather than time limit
Outcome
CLI successfully generates and validates Dockerfiles for Node, Python, and Go projects with auto-remediation of common build errors.
What I Learned
- Prompt engineering patterns for structured code generation
- Docker SDK for Python and programmatic image build APIs
- How to design resilient retry loops with exponential back-off
- Multi-stage Dockerfile optimisation for security and image size